2023-03-12 23:40:13
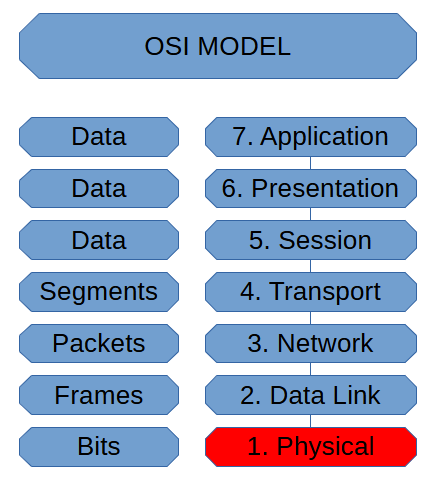
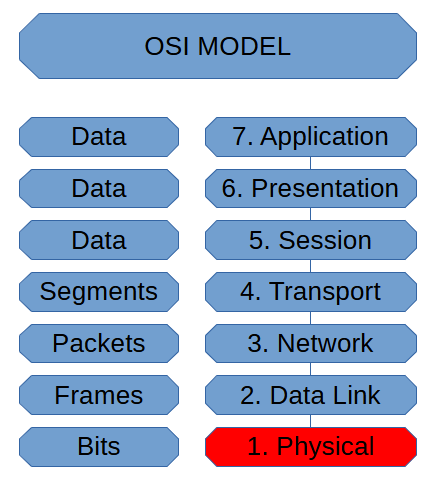
The Physical Layer is where we finally transmit our data. It is also when we initially receive data.
When we send data, we translate frames into bits and transmit them through the respective medium, be it twisted pai...
2023-03-11 21:08:48
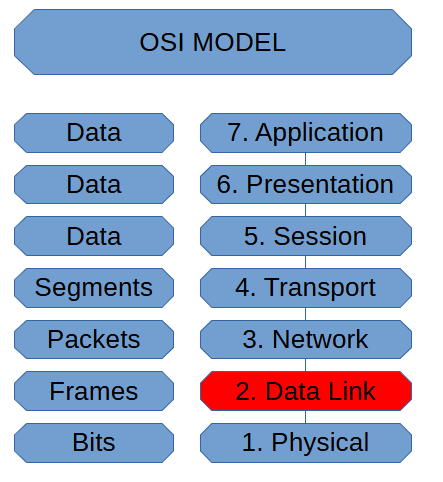
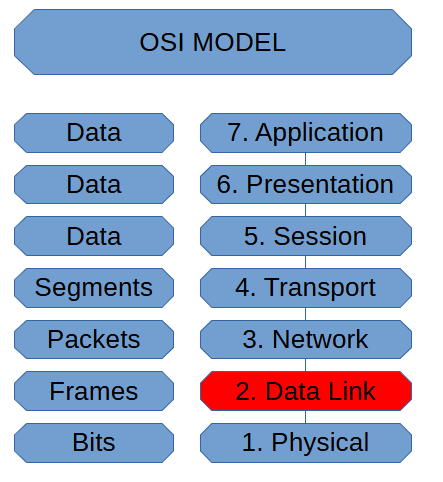
The Data Link is where we handle Media Access Control operations. It’s also how we deal with routing traffic. The Network Layer is where we do the IP Addressing, but when we IP route, we need to work with MAC Addresse...
2023-03-11 00:03:32
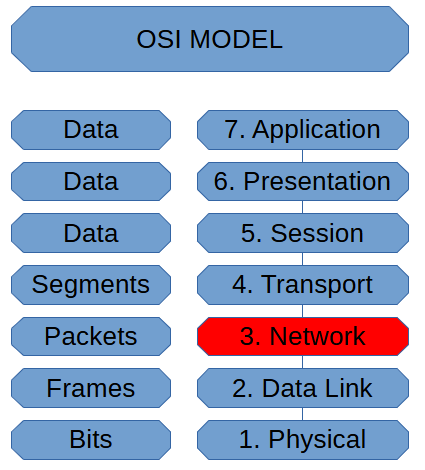
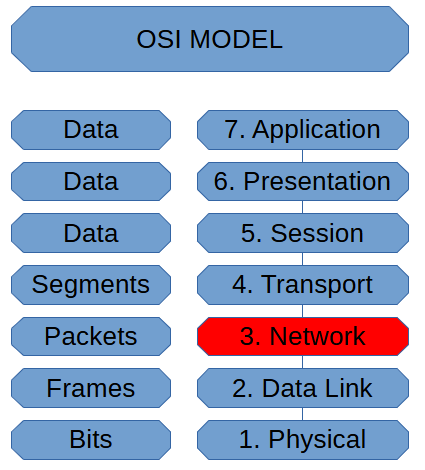
The Network Layer of the OSI Model is where we have packets. These packets don’t yet have a destination when your sending data.
While they don’t have a destination, this is where we give them an address to go. Wh...
2023-03-10 01:25:42
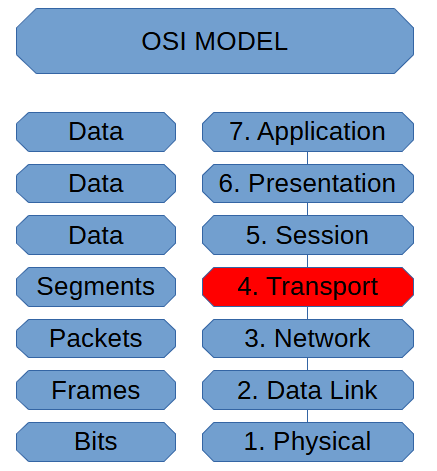
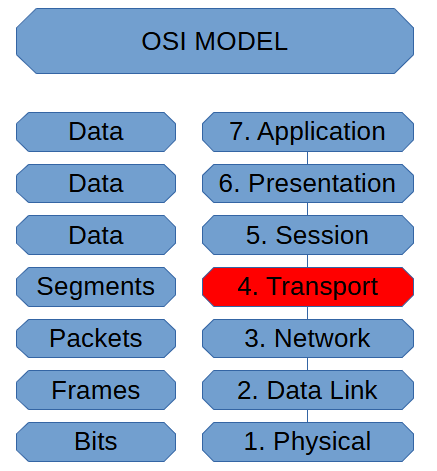
The Transport Layer of the OSI Model is where protocols such as UDP and TCP interact. We assign port numbers here as well. In this stage of the OSI Model, we deal with segments.
We now have a mechanism to determine i...
2023-03-08 20:31:00
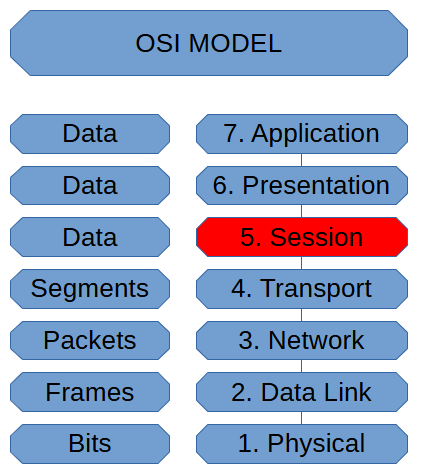
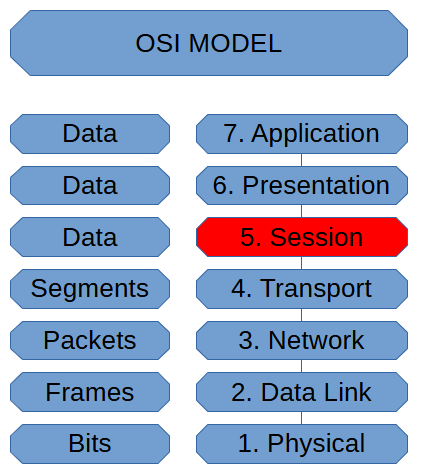
The session layer of the OSI Model is where sessions get managed. Being able to keep track of what data belongs to what process is a crucial part of being able to manage multiple sessions at the same time.
Authentica...
2023-03-07 22:39:07
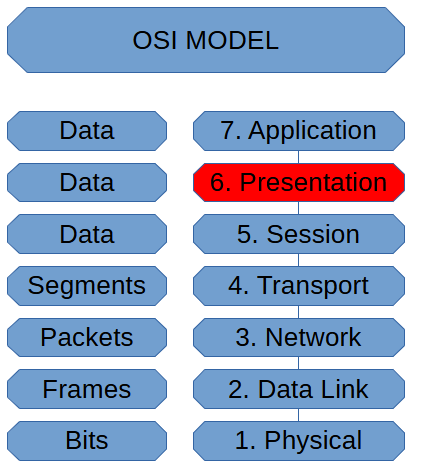
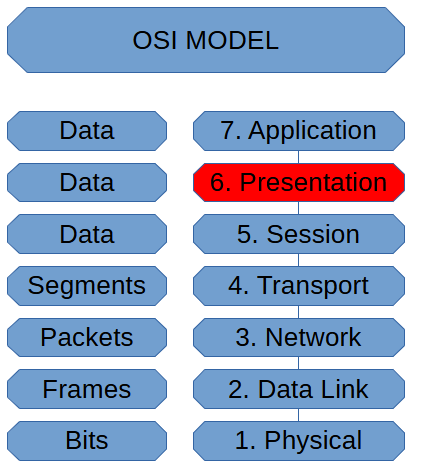
In the OSI Model, the Presentation Layer is where we format, compress, or encrypt, ensuring that the applications involved can use the data. This process ensures that the applications involved can use the data received....
2023-03-06 22:06:59
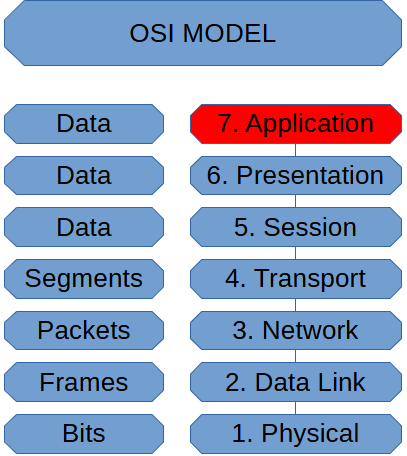
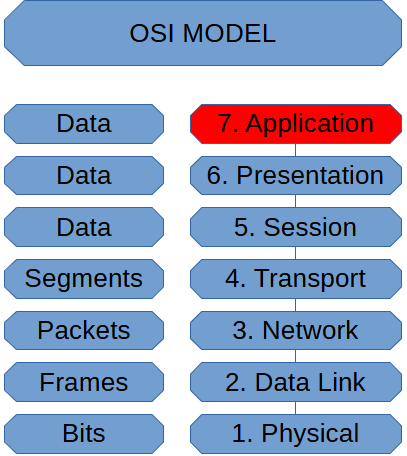
The Application layer is where Network Traffic Begins and Ends. When we initiate network traffic, we utilize an application to process network data to send.
In this stage of packet generation, we refer to what's gett...
2023-03-05 20:45:54
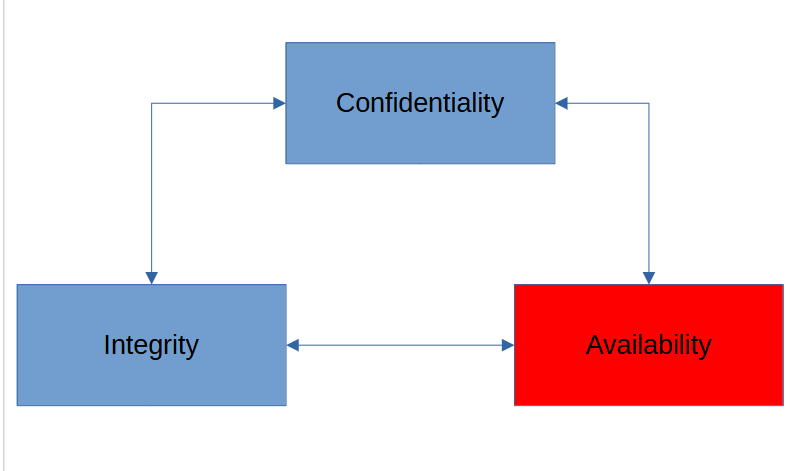
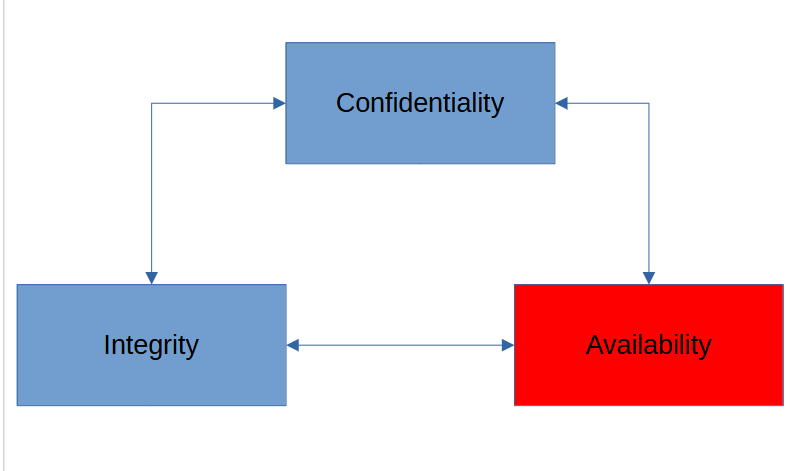
Availability is the final part of the CIA Triad. It is as crucial that we keep information available as it would be to keep it in the hands of only those authorized or that it hasn’t been corrupted or modified.
Hav...
2023-03-04 21:10:31
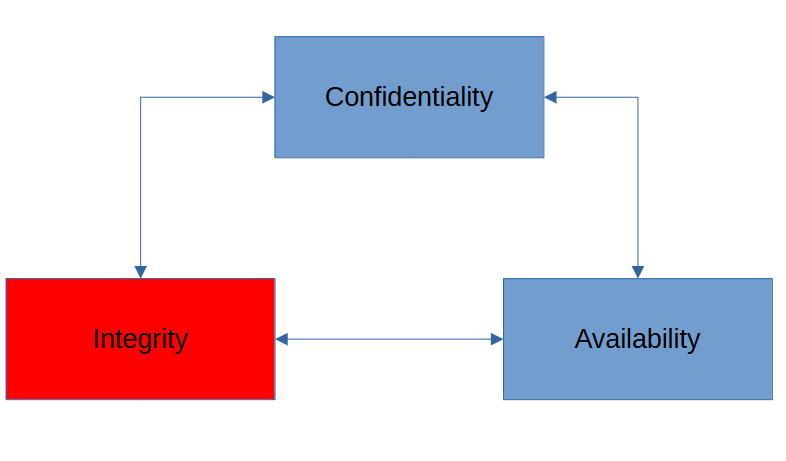
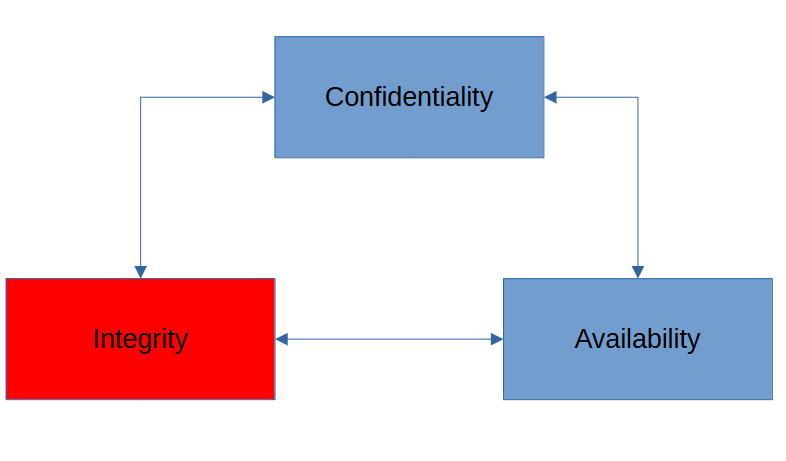
Integrity is the second aspect of cybersecurity. Integrity means we can prove that data is intact and is not corrupt or modified.
Not every case of data corruption is due to a threat actor. Other scenarios can be a f...
2023-03-03 18:58:54
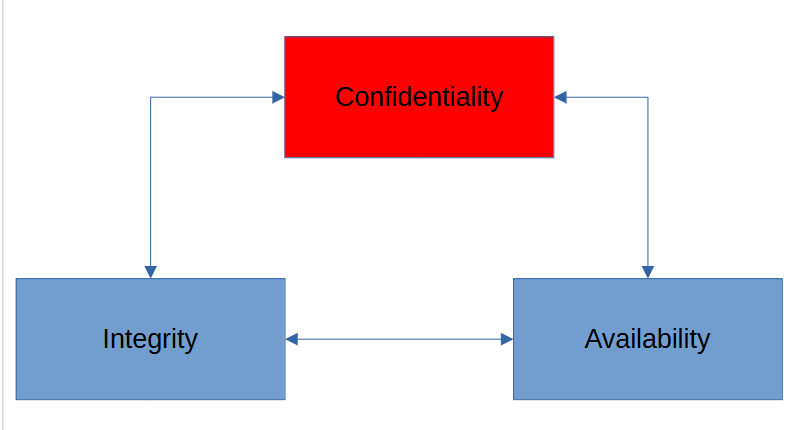
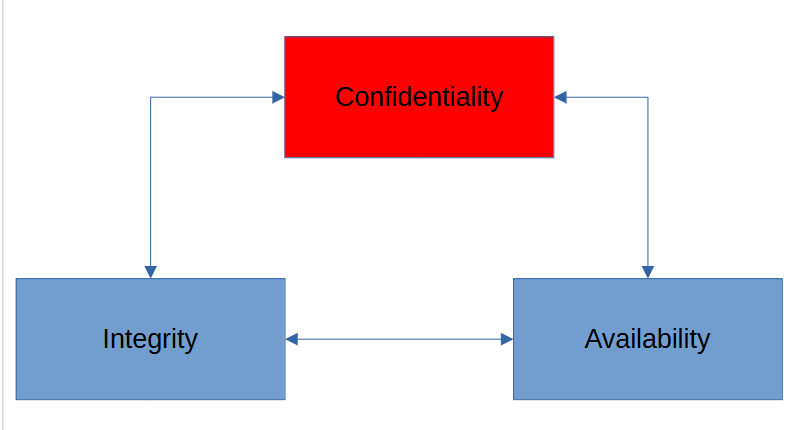
Confidentiality in the CIA triad is the ability to keep information in the hands of only authorized users. We achieve this through mechanisms such as access controls and encryption.
One way we could achieve confi...