2023-03-23 00:12:34
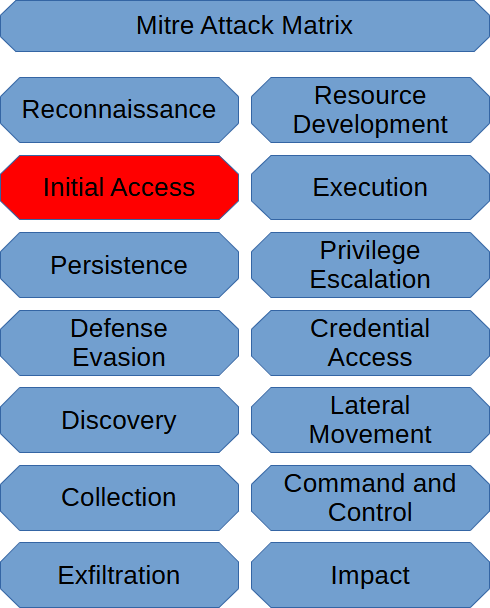
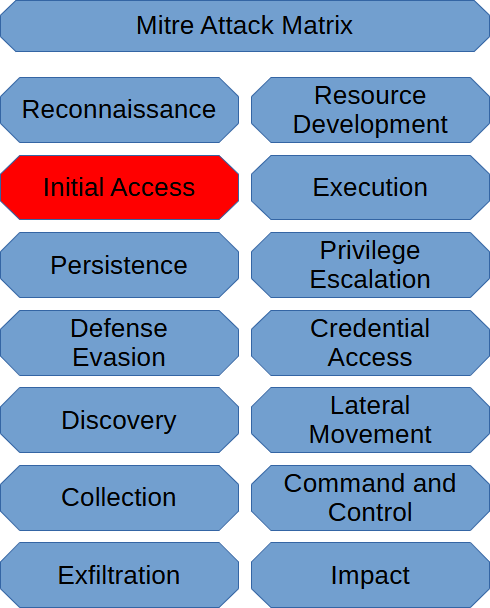
The Mitre Att&ck Matrix has defined nine techniques to cover initial access activities in a cyber attack.
Drive-by-Compromise is when a threat actor compromises a website to inject malicious code that executes wh...
2023-03-22 00:34:52
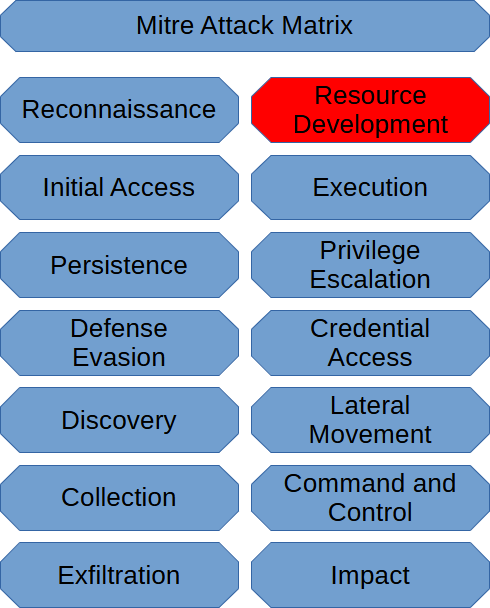
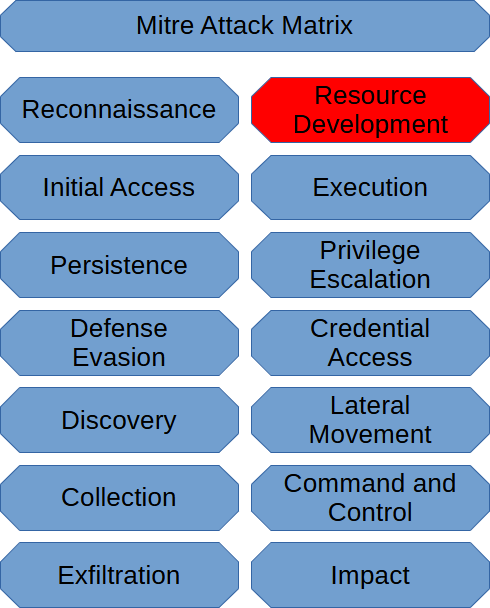
To define Resource Development, the Mitre Att&ck Matrix has defined seven techniques to cover the Resource Development techniques used in a Cyber Attack.
Acquire Infrastructure. The Acquire Infrastructure techniq...
2023-03-21 00:25:59

The MITRE Att&ck Matrix has specified ten techniques to classify as reconnaissance.
Active-Scanning means the threat actor used a tool such as Nmap to scan the network.
Gather Victim Host Information would mea...
2023-03-20 01:48:23
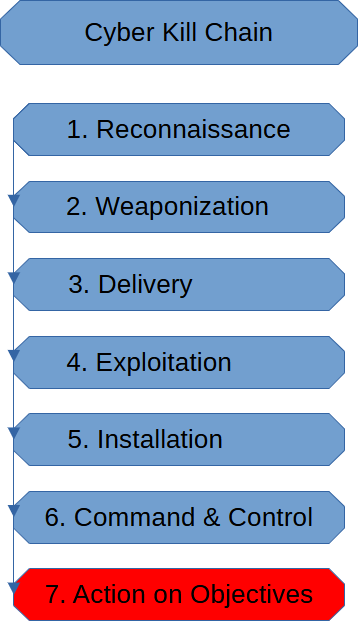
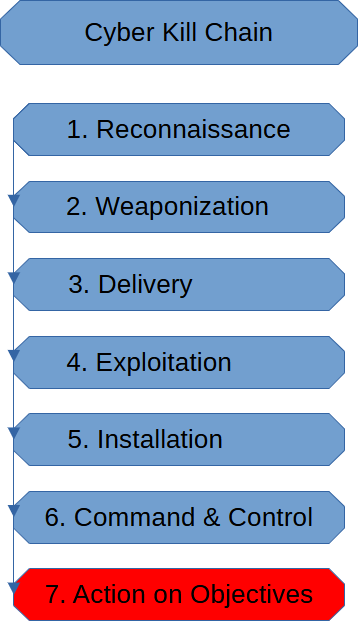
The Actions On Objectives Stage is the end of a Cyber Attack. The threat actor has achieved their goals.
In a ransomware attack, this would be the point it has spread as much as it could have until the attack termina...
2023-03-19 01:57:15
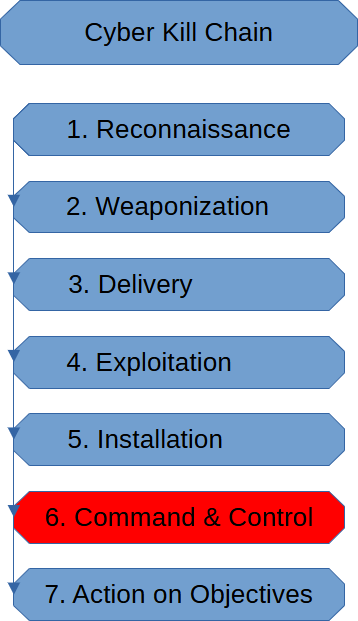
The Command & Control Stage of the cyber kill chain is when the threat actor establishes persistence.
Not every cyber attack deals with persistence the same. Ransomware might not be persistent as other cyber atta...
2023-03-18 02:30:27
The Installation Stage of the Cyber Kill Chain is when the threat actor establishes a foothold in the target's infrastructure. The victim of the attack should start to notice signs of an attack if they are monitoring.
...
2023-03-17 01:01:46
The Exploitation Stage is when we successfully execute the exploit we planned during the reconnaissance stage, which was prepared and delivered on the delivery stage.
We usually merely gain initial access as the resu...
2023-03-16 00:44:27
The Delivery Stage of the Cyber Kill chain is when the threat actor has decided on a method to deliver the malware the threat actor created.
One popular method of delivering malware is a variant of phishing. It may n...
2023-03-15 01:19:49
Weaponization in the cyber kill chain uses the intel the threat actor obtained from the reconnaissance stage to create a suitable piece of malware to infect their target.
The specific malware used will depend on the ...
2023-03-13 23:43:21
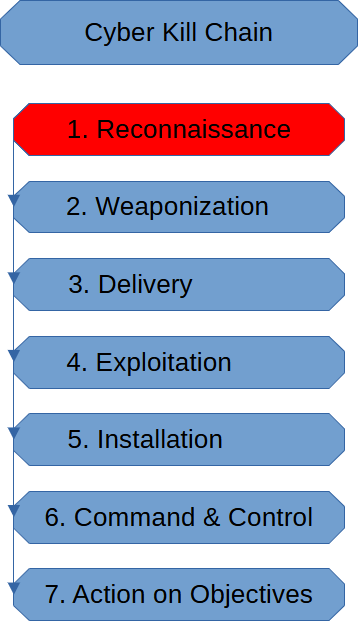
The Reconnaissance Stage of the Cyber Kill Chain is where the threat actor probes their target as thoroughly as he/she can so that the threat actor can gather as much intel as he/she can.
The Recon Stage is also wher...