LDAP Injection: What It Is and Why It Matters
LDAP Injection Vulnerabilities
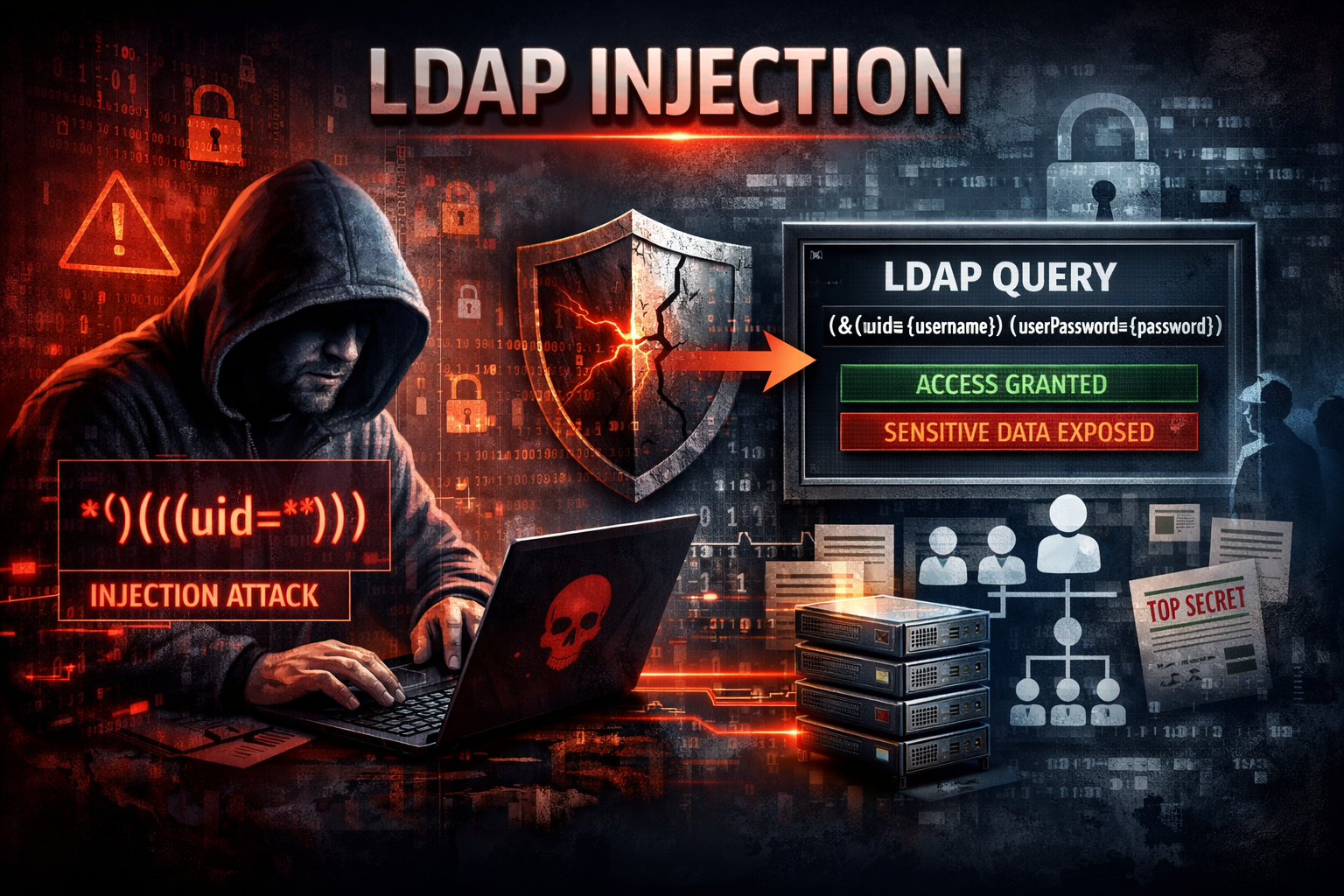
LDAP Injection is a type of security vulnerability that affects applications using the Lightweight Directory Access Protocol (LDAP) for authentication or directory queries (like Active Directory logins).
At its core, LDAP Injection happens when user input isn’t properly sanitized before being included in an LDAP query. Attackers can manipulate that input to change the query’s logic—potentially bypassing authentication or retrieving sensitive data.
⚠️ Why LDAP Injection Is Dangerous
This vulnerability can lead to serious security issues, including:
-
Authentication bypass
Attackers may log in without valid credentials by altering login queries. -
Data exposure
Unauthorized users could extract sensitive directory data (usernames, emails, roles). -
Privilege escalation
Attackers might gain higher-level access by modifying query conditions. -
Internal reconnaissance
LDAP directories often contain organizational structure and system info—valuable for attackers planning further attacks.
In environments using systems like Microsoft Active Directory, the impact can be especially severe because LDAP is central to identity and access management.
🛠️ How LDAP Injection Works (Simple Example)
A typical LDAP query might look like:
(&(uid={username})(userPassword={password}))
If user input isn’t sanitized, an attacker could input something like:
*)(|(uid=*))
This alters the query logic—potentially turning it into something that always returns true, allowing unauthorized access.
🛡️ How to Prevent LDAP Injection
Preventing LDAP Injection comes down to proper input handling and secure query design:
1. Use Parameterized Queries
Avoid building LDAP queries with string concatenation. Use safe APIs or frameworks that handle input binding properly.
2. Escape Special Characters
LDAP has special characters like:
* ( ) \ NUL
These must be escaped before being used in queries.
3. Validate User Input
- Restrict allowed characters (whitelisting > blacklisting)
- Enforce expected formats (e.g., usernames)
4. Apply Least Privilege
Ensure the LDAP account used by your app has minimal permissions—limit what an attacker could access even if exploited.
5. Use Strong Authentication Controls
- Multi-factor authentication (MFA)
- Account lockouts
- Monitoring for abnormal login behavior
6. Security Testing
- Perform regular penetration testing
- Use automated scanners to detect injection flaws
📌 Final Thoughts
LDAP Injection is less talked about than SQL Injection, but it can be just as dangerous—especially in enterprise environments. Since LDAP often controls authentication and directory access, a single vulnerability can expose an entire organization.
The good news: it’s highly preventable with proper input handling, secure coding practices, and least-privilege design.